Verifiable Information: An EU initiative to increase trust and reduce cost
Verifiable Information: An EU initiative to increase trust and reduce cost
20 November 2025
8
min read
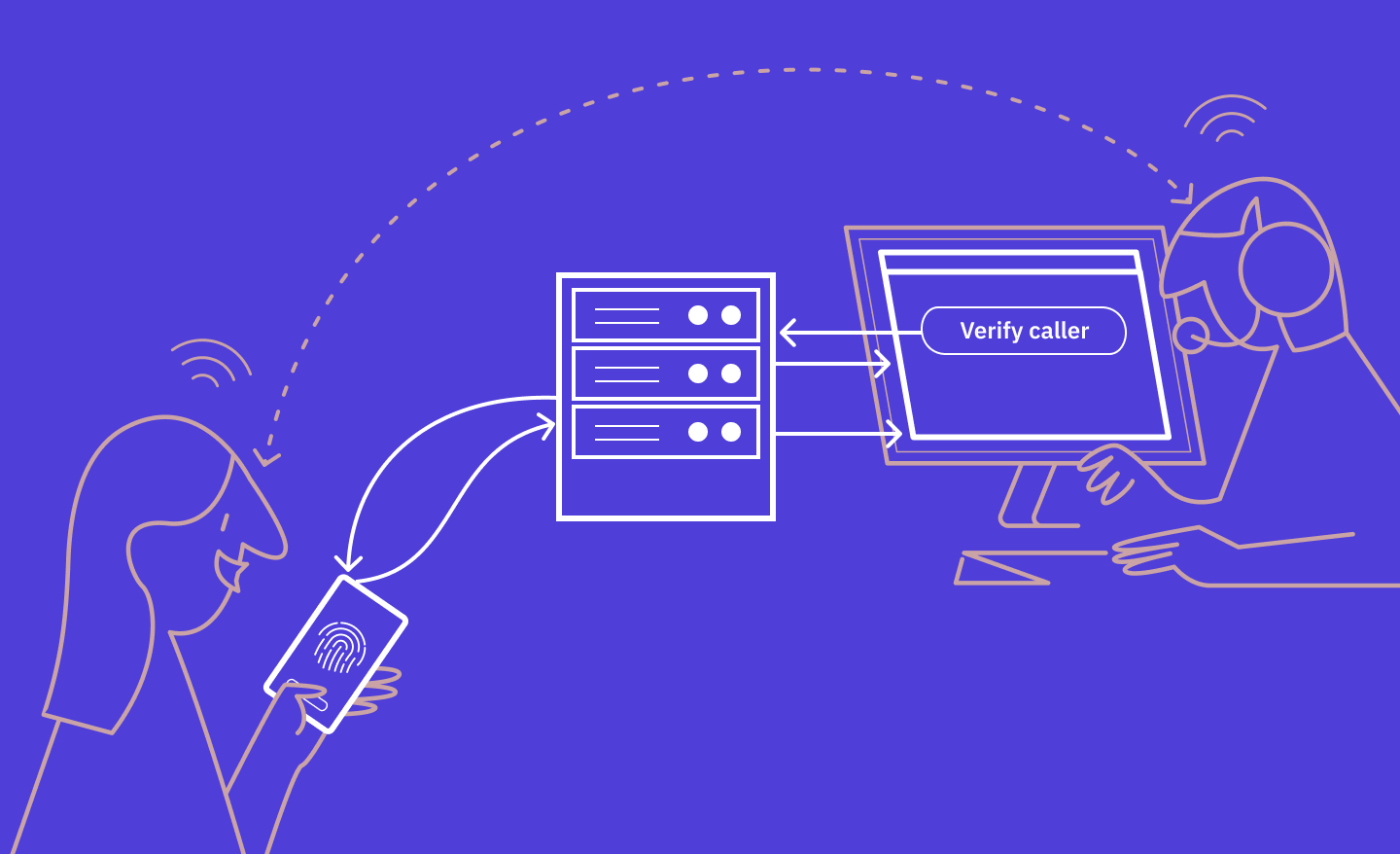
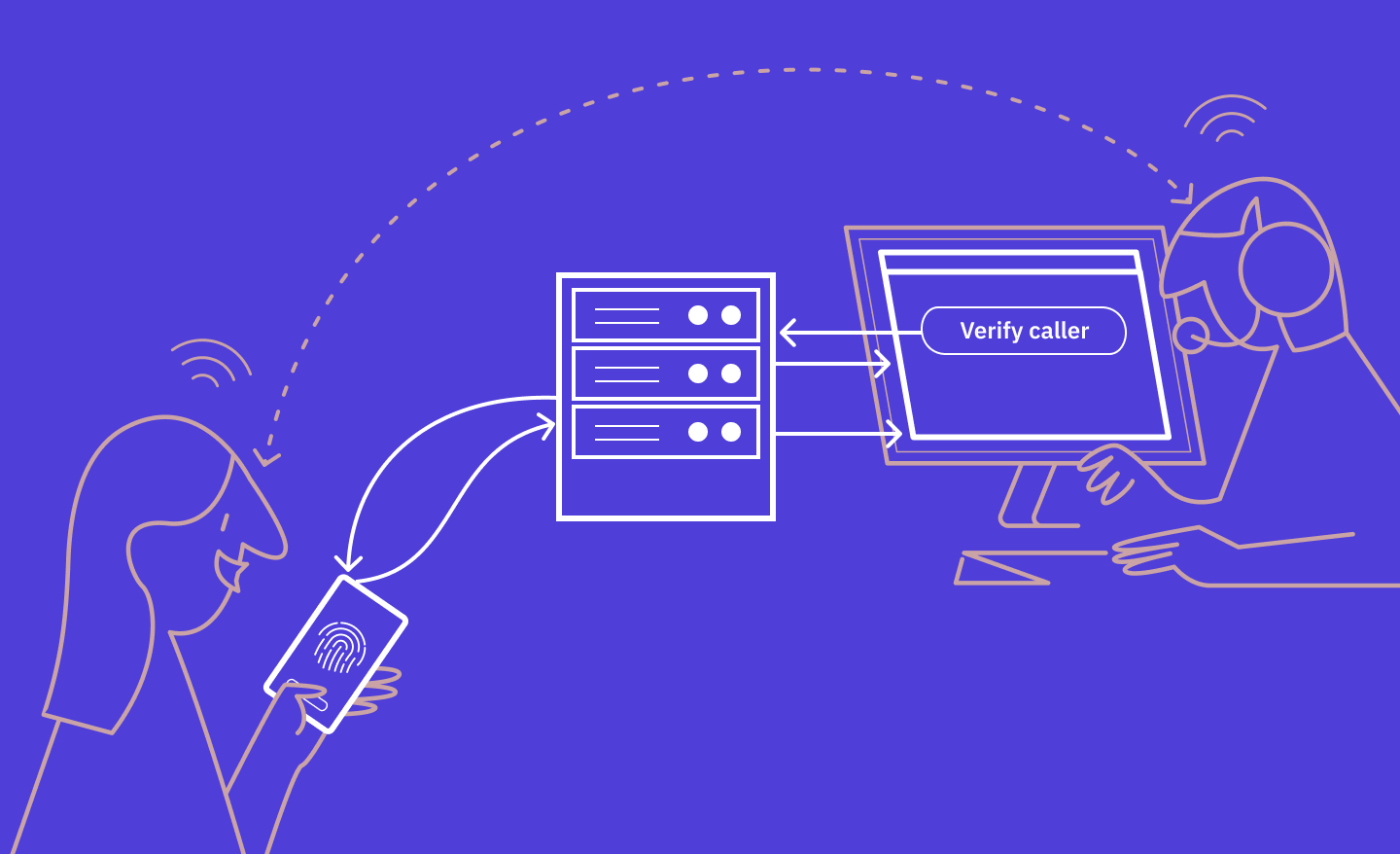
Why Caller Authentication is a Better Way to Verify Identity on the Phone


Why Caller Authentication is a Better Way to Verify Identity on the Phone
20 October 2025
2
min read
Digital Identity in Europe Depends on More Than Wallets


Digital Identity in Europe Depends on More Than Wallets
7 October 2025
2
min read
Practical Guide to FTN Compliance & the Idura Compliance Checker
Practical Guide to FTN Compliance & the Idura Compliance Checker
21 August 2025
3
min read
5 Reasons Verifiable Credentials Are Not Yet Widely Adopted


5 Reasons Verifiable Credentials Are Not Yet Widely Adopted
9 July 2025
3
min read
10 Use Cases for Verifiable Credentials


10 Use Cases for Verifiable Credentials
9 July 2025
4
min read
6 Business Benefits of Verifiable Credentials


6 Business Benefits of Verifiable Credentials
9 July 2025
5
min read
Why Signed Authorization Requests Elevate Your Security


Why Signed Authorization Requests Elevate Your Security
25 June 2025
4
min read
Private Key JWT: A Stronger Alternative for Client Authentication


Private Key JWT: A Stronger Alternative for Client Authentication
18 June 2025
3
min read
Securing Authentication Flows with JSON Web Encryption


Securing Authentication Flows with JSON Web Encryption
18 June 2025
3
min read
JSON Web Encryption: How It Works, Why Important, and When to Use It


JSON Web Encryption: How It Works, Why Important, and When to Use It
18 June 2025
7
min read
Want to Switch to a New eID Provider?


Want to Switch to a New eID Provider?
28 January 2025
2
min read
Multi-Factor Authentication: Definition, Use Cases, and Benefits


Multi-Factor Authentication: Definition, Use Cases, and Benefits
16 December 2024
5
min read
Passkeys: an Overview


Passkeys: an Overview
13 December 2024
7
min read
eIDAS Levels of Assurance in Different National eID Schemes


eIDAS Levels of Assurance in Different National eID Schemes
6 December 2024
4
min read
What is Authentication?
What is Authentication?
5 December 2024
6
min read
What is biometric authentication?
What is biometric authentication?
2 December 2024
5
min read
Zero-Knowledge Proofs: A Beginner's Guide
Zero-Knowledge Proofs: A Beginner's Guide
12 September 2024
10
min read
Getting Started with iDIN: The Complete Guide for Businesses


Getting Started with iDIN: The Complete Guide for Businesses
1 August 2024
3
min read
How to Authenticate Callers with Twilio, CIBA, and the Swedish BankID Phone Authentication


How to Authenticate Callers with Twilio, CIBA, and the Swedish BankID Phone Authentication
4 July 2024
10
min read
An Introduction to Client Initiated Backchannel Authentication (CIBA)
An Introduction to Client Initiated Backchannel Authentication (CIBA)
31 May 2024
4
min read
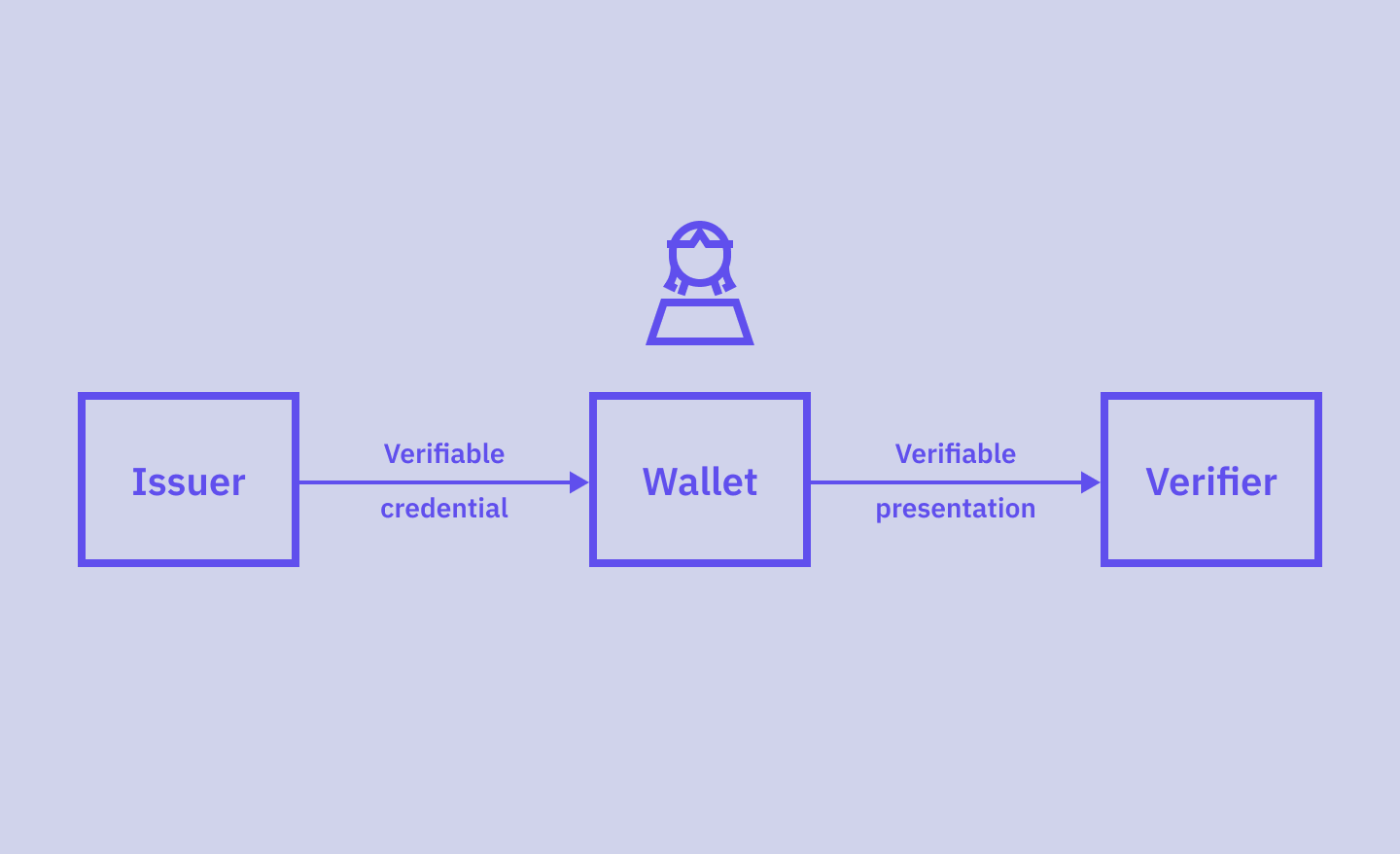
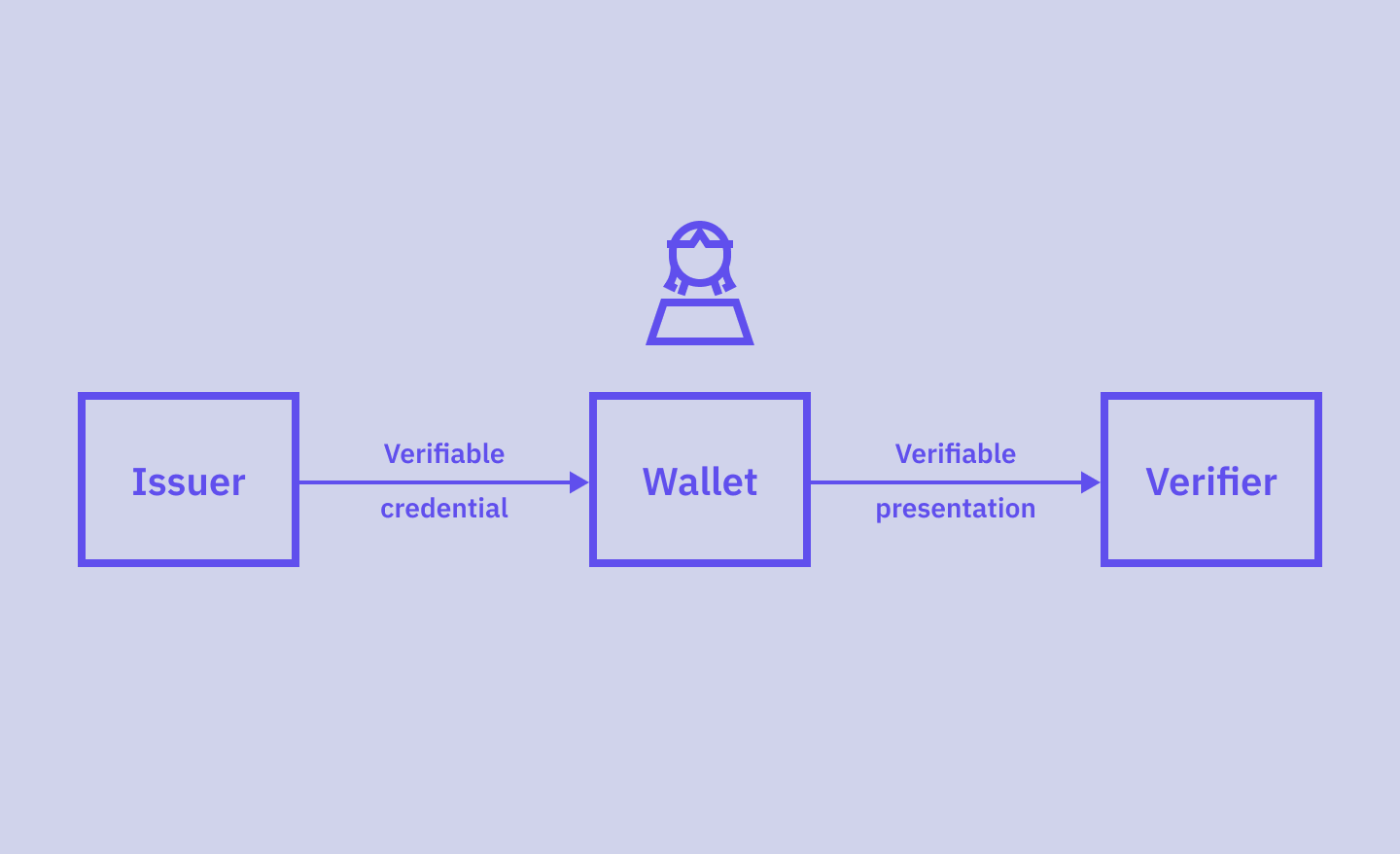
What Are SD-JWT-based Verifiable Credentials?
What Are SD-JWT-based Verifiable Credentials?
21 March 2024
7
min read
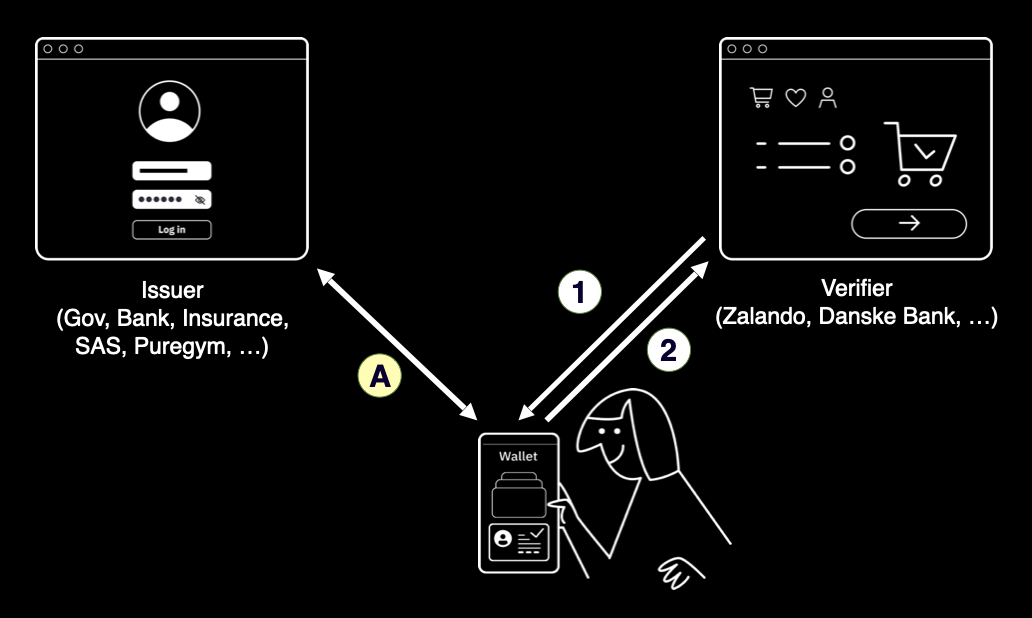
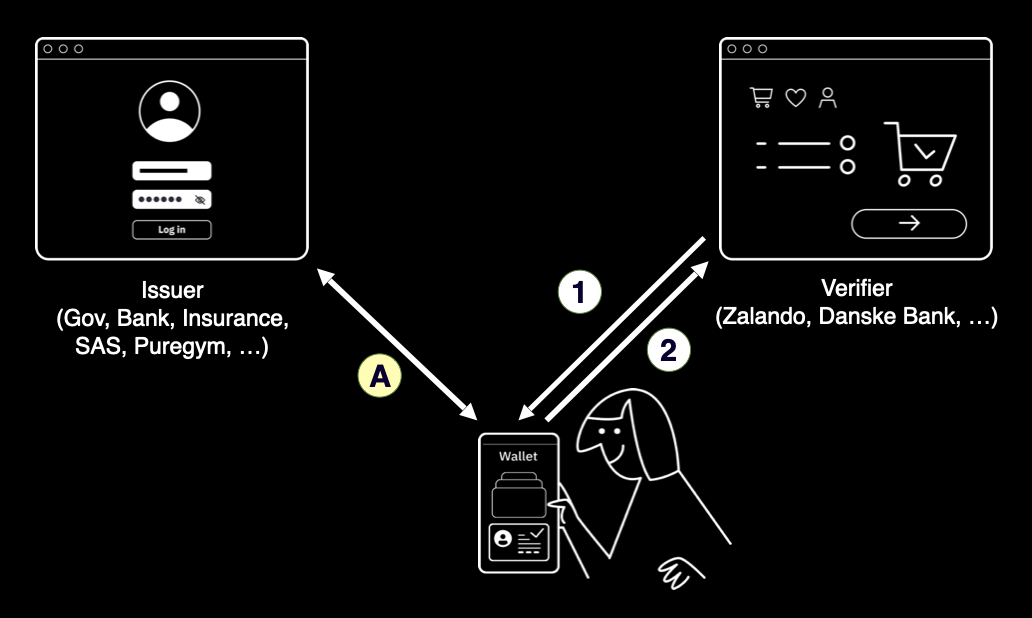
Verifiable Credentials: A Glossary (For Everyone)
Verifiable Credentials: A Glossary (For Everyone)
1 March 2024
7
min read
Understanding JWT Validation: A Practical Guide with Code Examples
Understanding JWT Validation: A Practical Guide with Code Examples
22 January 2024
11
min read
How To Use Fiddler to Debug Authentication Flows
How To Use Fiddler to Debug Authentication Flows
12 December 2023
9
min read
Use Cases for Address Registry Lookups: From UX to Fraud Detection


Use Cases for Address Registry Lookups: From UX to Fraud Detection
25 October 2023
4
min read
Introducing Custom HTML & CSS for Login Flows
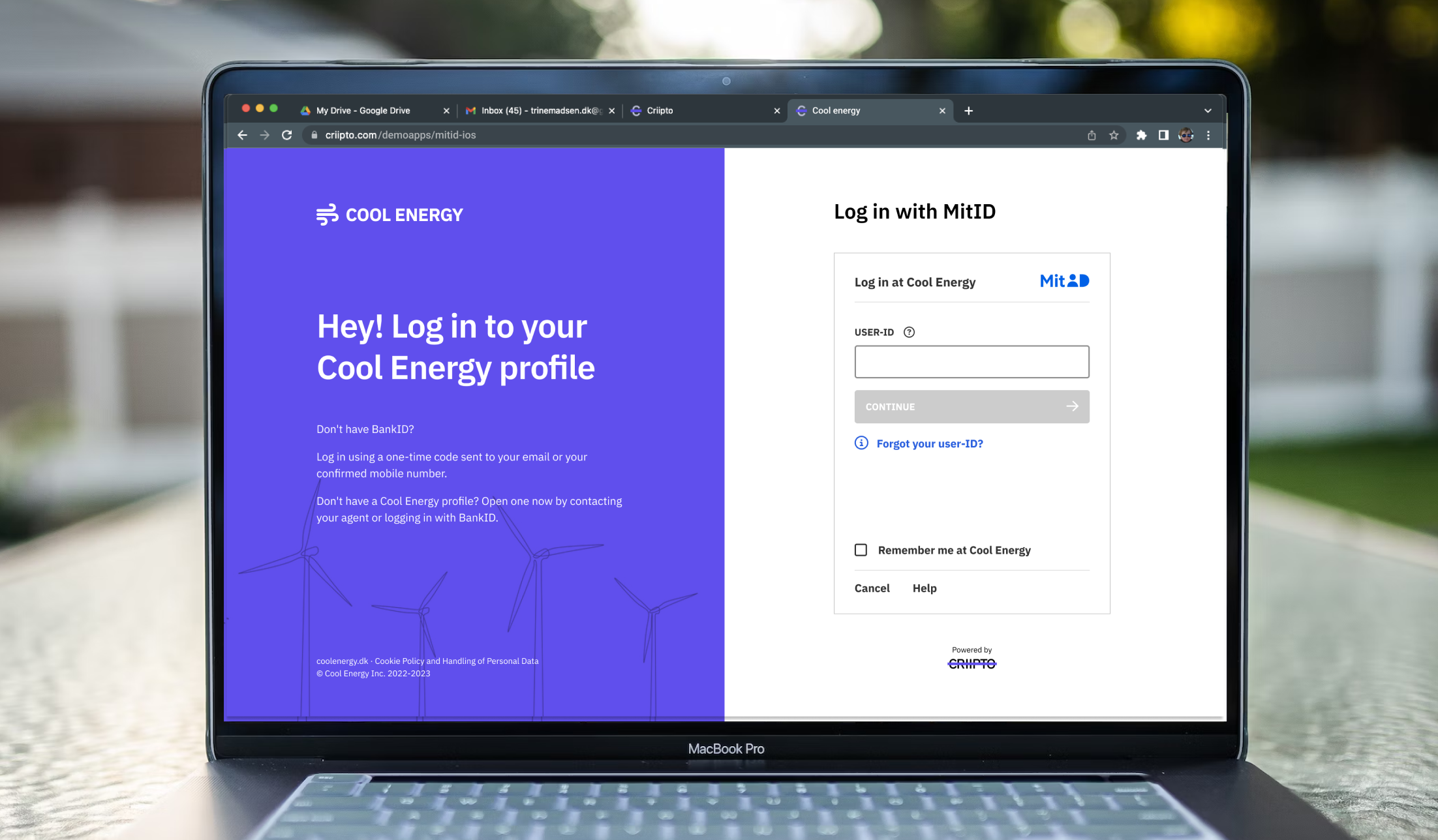
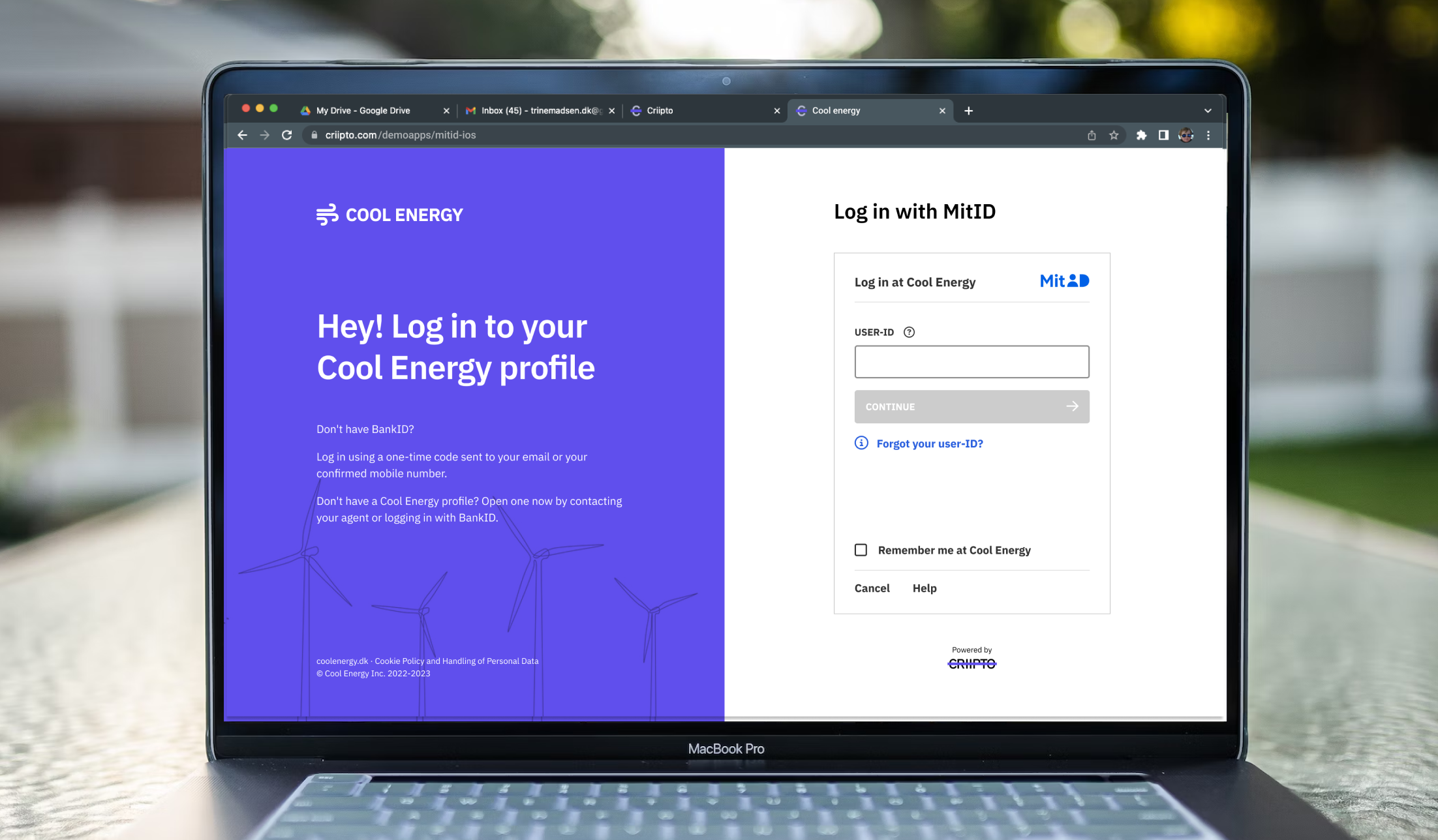
Introducing Custom HTML & CSS for Login Flows
2 October 2023
3
min read
Persistent User Identification with eIDs


Persistent User Identification with eIDs
7 June 2023
4
min read
User Authentication: Comparing Session-based and Token-based Implementations


User Authentication: Comparing Session-based and Token-based Implementations
26 May 2023
11
min read
Strong Customer Authentication 101


Strong Customer Authentication 101
1 May 2023
2
min read