How Exactly Does Caller Authentication Work?
By Daniel Gniazdo on 6 March 2026
4 min read
Caller authentication aims to answer just one question: Is the caller who they say they are?
But how you do that has changed quite a lot over the years.
Let’s take a look at a few traditional methods, then discuss how eID-based caller authentication works today.
Traditional caller authentication methods
Historically, companies have relied on several alternatives to verify callers:
- Security questions: “In what city were you born?” These are easy to remember but also easy to guess. (In some cases, fraudsters can pass these checks over 90% of the time.)
- PINs or passcodes: Punch in your preset code via keypad. This approach is vulnerable to phishing and social engineering.
- National ID numbers: “Last four digits of your social security number?” The problem here is that knowing such details doesn’t really prove you are that person. National IDs are easily exposed in everyday conversations or leaked in mass breaches.
- One-time passwords (OTPs): One-off codes sent to the user’s number or email. While better than static passwords, they’re still not immune to SIM swaps and phishing attacks.
- Caller ID matching via Automatic Number Identification (ANI): “Does the caller’s number exist in our system?” This does little to prevent calls from stolen phones or number spoofing.
- Voice biometrics: This tries to automatically identify and match the caller’s voice to an existing customer. Unfortunately, modern AI voice cloning is making this method far less reliable than it used to be.
Each of these classic methods comes with its own trade-offs. Some are easy to implement but less secure. Others offer better security but create additional friction.
But there is a better way.
The rise of eID-based caller authentication
Increasingly, businesses are turning to eID-driven caller authentication.
Instead of asking preset questions or shuffling codes around, this lets users prove their identity with the same national eID app they’re already using. Plus, the entire process happens on their own device, separate from the call itself.
Because of that, using eIDs for caller authentication is simultaneously more secure and more user-friendly than traditional methods.
On a call, this type of authentication can be triggered in two primary ways:
- By the phone system, either automatically for existing customers or after the caller provides an identifier through the IVR (interactive voice response) menu. This can even happen while the caller is in a phone queue.
- By the call center agent, as part of the conversation with the caller. This gives agents some discretion over whether and when to initiate the CIBA flow.
In both cases, the rest of the flow is essentially identical once initiated.
Now let’s look at what actually happens at that point.
The three-party process
Every caller authentication flow that relies on eIDs involves three parties:
- The agent: The call center agent (or system) who triggers the authentication request.
- The caller: The person who needs to authenticate themselves using their eID.
- The authorization server: The “middleman” that handles the verification itself.

Here’s what each party does and sees on their end.
What does the agent experience?
From the agent’s perspective, everything’s quite straightforward.
All they really do is punch in the caller’s identifier to start the CIBA flow. Then they just…wait.
After the caller successfully authenticates, the agent sees a “Verified” status on the screen.
That’s it.
The agent can simply proceed to help the now-verified customer.
What does the caller experience?
The caller’s side is a bit more involved but not all that different from how they’d use their eID in any other situation.
First, depending on the eID, they’ll see a push notification on their phone requesting to start the authentication process.
As part of this step, they may also be asked to confirm whether they actually called the company. This helps prevent inbound fraud and gives the caller a chance to cancel the flow if needed.
If the caller accepts the request, the rest is a familiar process: The caller uses their national eID app to verify themselves as normal.
Then they can talk to the call center agent, having proven their identity.
What happens behind the scenes?
In short: A whole lot of stuff.
The authorization server handles the bulk of the process, relaying requests and notifications between the two other parties.
The flow looks something like this:
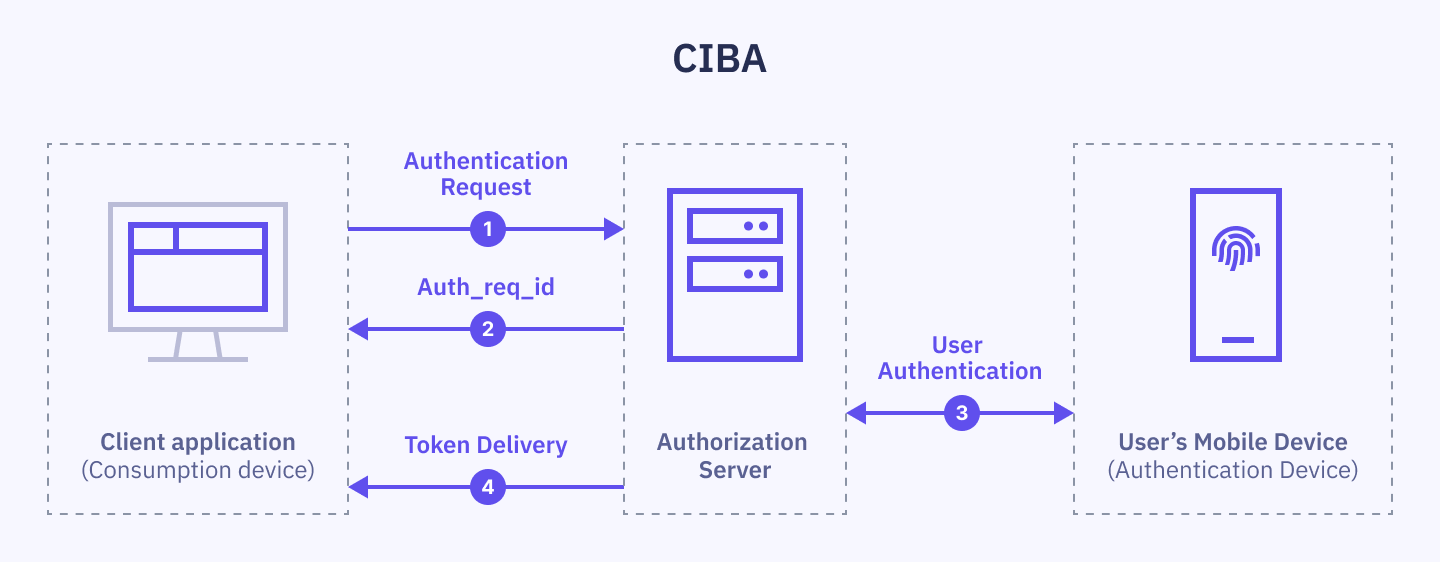
- When the agent initiates things on their end, the authorization server receives an authentication request with the caller’s identifier (among other things).
- The server replies with a unique “authorization request identifier” as confirmation and to help track the request.
- The server relays the request to the caller’s device and prompts them to authenticate.
- Once the caller authenticates, the server relays this to the agent’s system in the form of special tokens that prove the caller’s identity.
For a more technical walkthrough, see: An Introduction to Client Initiated Backchannel Authentication (CIBA)
What do you need to get started?
If your company wants to implement eID-based caller authentication, you’ll need a few things:
- Compatible call center platform: Your existing phone system should support CIBA flows.
- Customer identifiers: You need a way to match the caller to a unique identifier that can initiate the process.
- An eID broker: In many countries, eID verification requires a certified broker like Idura to handle the legal and technical implementation.
Caller authentication has evolved a lot since the early days of security questions. National eIDs offer a future-proof way forward.
And it certainly doesn’t hurt that eID adoption is near-universal in the Nordics. The tools you need are already in your customers’ pockets.
Ready to make your service calls safer and simpler?
Caller authentication is already available with Norwegian and Swedish BankID, with the Danish MitID coming soon.
Start testing for free today or contact our sales team to learn more.
These Related articles

Zero Friction = Zero Assurance: The Case for eID Caller Authentication
Caller Authentication: Idura Launches New Identity Solution with MobilePay
