Zero Friction = Zero Assurance: The Case for eID Caller Authentication
By Daniel Gniazdo on 20 April 2026
3 min read

When interacting with customers, businesses generally want as little friction as possible.
This is especially true for call centers, where increasing customer satisfaction and reducing call duration are often explicit targets.
But eliminating all friction on a call would technically require skipping any form of identity verification. Clearly, that would be a terrible idea on sensitive or high-risk calls.
So the real question is: How do you strike a balance between friction and trust?
Let’s see why eID caller authentication may just be the answer.
Why call centers try to reduce friction
The job of a call center agent is to resolve the customer’s problem as quickly and efficiently as possible.
As such, it’s no surprise that many call center KPIs and metrics focus on reducing handling time and increasing customer satisfaction. Here are just a few examples:
- Average Handling Time (AHT): How long does it take agents to handle a customer call?
- Cost Per Call (CPC): What does an average customer call cost the company?
- Customer Effort Score (CES): How much effort does the call require from the callers themselves?
- Customer Satisfaction (CSAT): How satisfied is the customer with the interaction?
These metrics put understandable pressure on call centers to keep calls short and make them frictionless for customers.
The problem with zero friction
Taken to the extreme, trying to minimize friction may undermine efforts to reduce fraud and keep calls secure.
A call center might be tempted to do only minimal caller identity verification or stop doing it altogether. After all, asking customers security questions or making them check their inbox for a one-time password is bad news for “time-on-call” and “customer effort” metrics.
But identity verification isn’t exactly a nice-to-have step. It’s critical for making sure the caller is who they claim to be. In some cases, robust caller verification is also a regulatory requirement as part of know-your-customer laws.
In short, removing all friction should rarely be your only priority.
So, how much friction is okay, then?
Legible friction = acceptable friction
The truth is, your customers may be perfectly fine with a bit of friction, as long as they can understand its benefits and the reasons behind it.
In fact, callers likely even expect a degree of friction when it comes to identity verification, because they know that the alternative is an impersonator potentially gaining easy access to their accounts, finances, or sensitive personal information.
Seen in this light, friction actually introduces trust into the process.
As this CX Today article puts it:
“The real tradeoff isn’t friction versus experience. It’s harm versus trust.”
That’s why your goal isn’t to remove all friction, but to make it clear why friction exists and how it builds trust on both ends of the call. The article calls this “legible friction” and argues that it’s a much better target than “zero friction.”
With that in mind, you need to find the right balance between security, trust, and friction.
And eID-based caller authentication may just be the way to do exactly that.
eID caller authentication: the best of both worlds
There are many different ways to verify a caller’s identity.
In most cases, there’s a natural trade-off between customer experience, verification speed, and level of security.
For instance, asking someone for their national ID number is easy and quick, but it’s highly insecure. National ID numbers are often leaked and can be overheard or exposed in a myriad of different ways. That’s why national ID numbers are great for identifying a customer but not for verifying them.
One-time passwords, on the other hand, are more secure, but callers have to first wait for a password to show up via SMS or email, hunt for it in their inbox, and then type it in while on call, which doesn’t exactly do wonders for speed or user experience.
Caller authentication via eIDs is different: It lets companies verify customers securely and with little added friction.
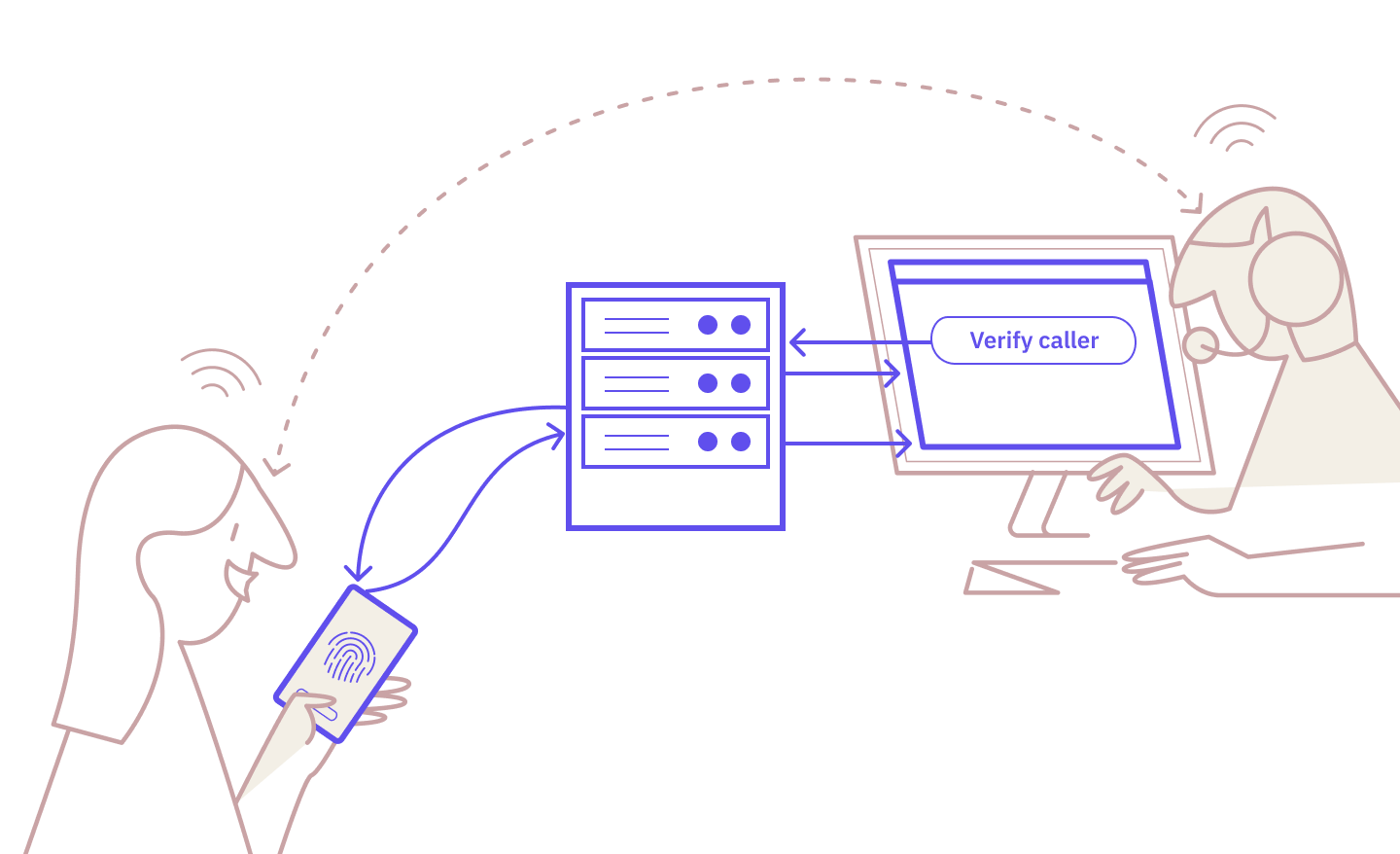
That’s because this approach relies on national eID apps that most citizens already regularly use. The process is straightforward:
- The call center agent triggers the authentication request.
- The caller receives the request in their eID app and verifies on their device.
- The agent sees the verified status, and the call continues.
While it’s not completely effortless, eID caller authentication arguably offers the best balance between trust and friction:
| eID Caller Authentication | Security Questions | National ID Numbers | One-Time Passwords | PINs | Voice Biometrics | |
| Security strength | HIGH | LOW | LOW | MODERATE | LOW | HIGH |
| Fraud resistance | STRONG | WEAK | WEAK | MODERATE | WEAK | MODERATE |
| Audit trail | STRONG | WEAK | WEAK | WEAK | WEAK | STRONG |
| Caller experience | NEUTRAL | NEGATIVE | POSITIVE | NEGATIVE | NEUTRAL | POSITIVE |
| Verification speed | FAST | SLOW | FAST | MODERATE | FAST | FAST |
| Implementation effort | MODERATE | LOW | LOW | MODERATE | LOW | HIGH |
| Customer type | EXISTING & NEW | EXISTING ONLY | EXISTING ONLY | EXISTING ONLY | EXISTING ONLY | EXISTING ONLY |
Voice biometrics is a close second, but it’s increasingly vulnerable to AI deepfakes and requires more effort to implement.
eID caller authentication is also the only verification method that lets companies verify brand-new callers, because it doesn’t rely on existing customer records.
So if your goal is legible friction instead of zero friction, eID-based caller authentication truly gives you the best of both worlds.
Ready to make your service calls safer and simpler?
Caller authentication is already available with Norwegian and Swedish BankID, with the Danish MitID coming soon.
Start testing for free today or contact our sales team to learn more.
These Related articles
Caller Authentication: Idura Launches New Identity Solution with MobilePay

Why Identification Is Not The Same As Verification
