Caller Authentication vs. One-Time Passwords
By Daniel Gniazdo on 23 March 2026
3 min read

One-time passwords (OTPs) are a standard security feature in online apps and services.
When people try to sign in, they receive a one-off code by SMS or email (or via an authenticator app, if they’re fancy). They type it into a verification form, and the site lets them in.
This works well for logging into websites, but it can introduce unnecessary friction while on a phone call.
Let’s look at how OTPs compare to eID-based caller authentication.
How one-time passwords work on calls
When a caller needs to be verified, the system or agent sends a time-limited code to the phone number or email address on file.
The caller types in the code on their dialpad as a response to an IVR prompt or while the contact center agent is standing by.
Either way, the system checks whether the entered OTP is correct, and the call can continue.
In rare cases, the agent may request the caller to speak the OTP out loud. This is generally bad practice, as it may normalize sharing your one-time password with others (something that is strongly discouraged because that’s exactly how OTP-based scams work).
One-time passwords are familiar to anyone used to signing into digital services or confirming purchases online.
But phone calls introduce unique friction into the process. The caller is already using the phone to speak with the agent, so having to check their SMS or email for the OTP code takes time and requires switching context mid-conversation.
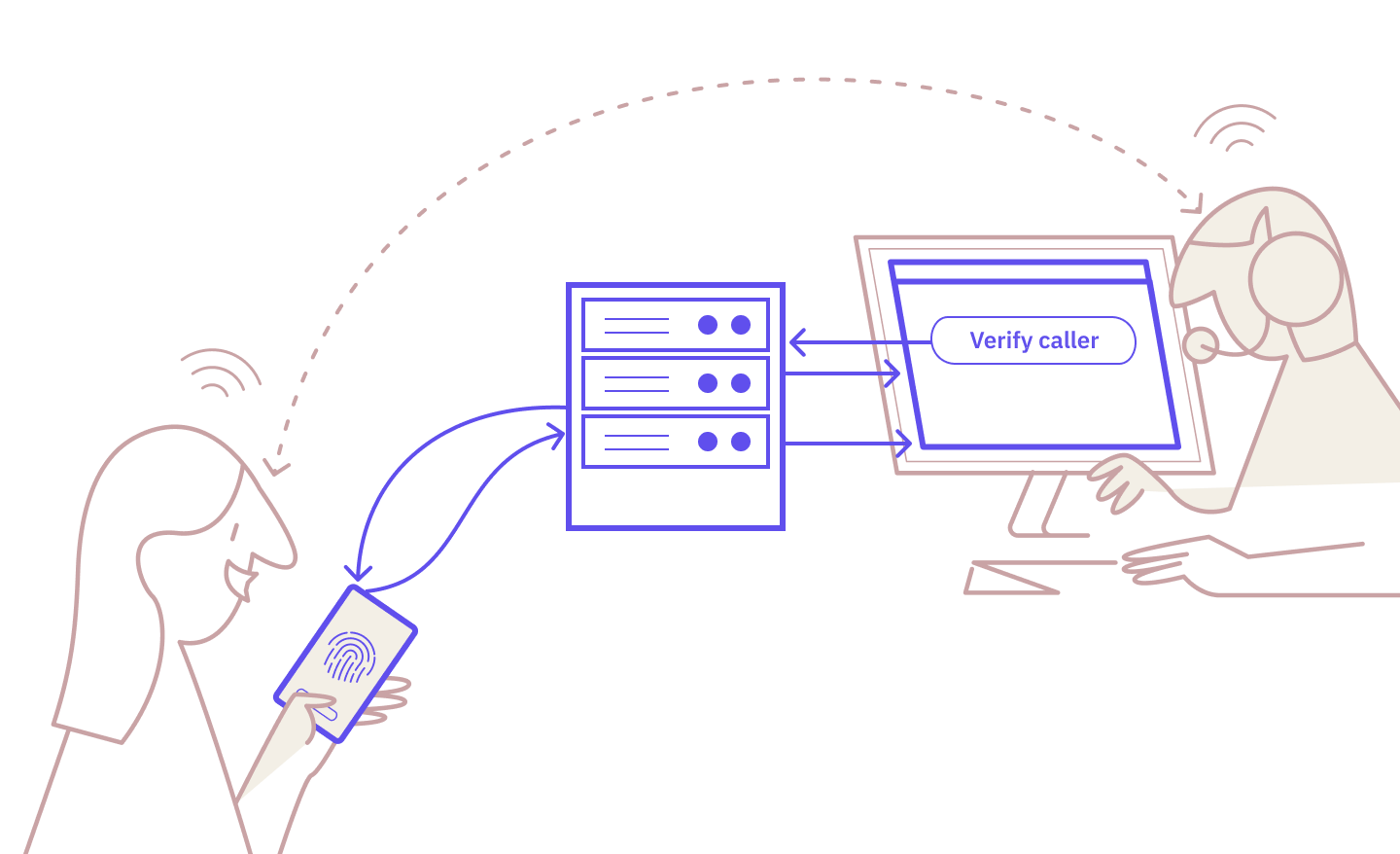
How eID caller authentication works
eID-based caller authentication relies on national eID apps that most citizens already use.
Here’s how the process looks:
- The agent triggers the authentication request.
- The caller receives the request in their eID app and verifies on their device.
- The agent sees the verified status, and the call continues.
It’s familiar, straightforward, and robust.
For a more comprehensive look, read: “How Exactly Does Caller Authentication Work?”
Caller authentication vs. one-time passwords: side-by-side
Here is how one-time passwords compare to eID caller authentication.
|
One-Time Passwords |
eID Caller Authentication |
|
|
Security strength |
Moderate: One-off, time-limited code tied to a specific number/email |
High: eID-based cryptographic verification |
|
Fraud resistance |
Moderate: Vulnerable to SIM swapping and real-time phishing |
Strong: Requires the caller’s physical device and eID app |
|
Audit trail |
Weak: Logs that the correct OTP was entered but not by whom |
Strong: Cryptographic proof of verification (who and when) |
|
Caller experience |
Negative: Wait for OTP mid-call and enter it under time pressure |
Neutral: Familiar eID-based flow with a few extra steps |
|
Verification speed |
Moderate: Depends on delivery timing and typing speed |
Fast: Seconds from the agent triggering to the caller verifying |
|
Implementation effort |
Moderate: Integration with SMS or email gateway and code generation |
Moderate: Integration with an eID provider via API or broker |
|
Customer type |
Existing only: Needs the customer’s email or phone number on file |
Existing and new: Anyone with an eID can be verified |
When do one-time passwords make sense?
OTPs offer more secure verification than either security questions or national ID numbers. The underlying method is sound: One-off codes are dynamically generated and limited to a short verification period.
The problem with OTPs is the delivery channel itself.
SMS messages are vulnerable to SIM swapping and SS7 attacks, while emails are typically unencrypted and may be wiretapped or read by anyone with access to a compromised inbox. And then there’s phishing, where a third party impersonates someone you trust and asks for the one-time password on the phone.
Beyond these security risks, OTPs aren’t particularly convenient for the caller who has to juggle an agent, an inbox or SMS, and typing a code via a dialpad.
The next step
One-time passwords were primarily designed for the digital world of logging into websites and approving transactions.
But phone calls are a different environment. Asking callers engaged in a conversation to wait and check for a code and remember it long enough to punch it in adds fully avoidable friction.
eID-based caller authentication handles verification through a familiar app on the caller’s device without delivery delays or dealing with dialpads.
If you’re looking for a verification method that’s better-suited for phone calls, we can help you get started.
Ready to make your service calls safer and simpler?
Caller authentication is already available with Norwegian and Swedish BankID, with the Danish MitID coming soon.
Start testing for free today or contact our sales team to learn more.
These Related articles

Zero Friction = Zero Assurance: The Case for eID Caller Authentication
Caller Authentication: Idura Launches New Identity Solution with MobilePay
