Caller Authentication vs. Security Questions
By Daniel Gniazdo on 13 March 2026
2 min read

Security questions have long been the standard way to verify people on the phone.
The call center agent asks for your city of birth or the last four digits of your credit card number, and if your answer matches, you’re in.
But times are changing, and secure authentication methods are replacing security questions.
eID-based caller authentication is one such method. Instead of asking what you know, it confirms who you are directly via standardized national eIDs.
Let’s look at the way each method works and how they compare.
How security questions work
When people first sign up for an account with, say, a bank or an insurance company, they’ll often be asked to provide a “secret” answer to a security question.
Classic questions include:
- What is your mother’s maiden name?
- What was the name of your first pet?
- What city were you born in?
- …and so on.
Their answer gets logged in the system and linked to their account.
The next time a call center agent needs to verify that person’s identity, the agent will request their answer to the security question and match it to the database.
While this setup is easy to implement, it comes at a cost.
Security questions are an ineffective and insecure way to verify callers.
Not only are the answers typically easy to figure out, but people often forget their own question-answer pairs, which causes friction.
How eID caller authentication works
eID-based caller authentication relies on national eID apps that most citizens already use.
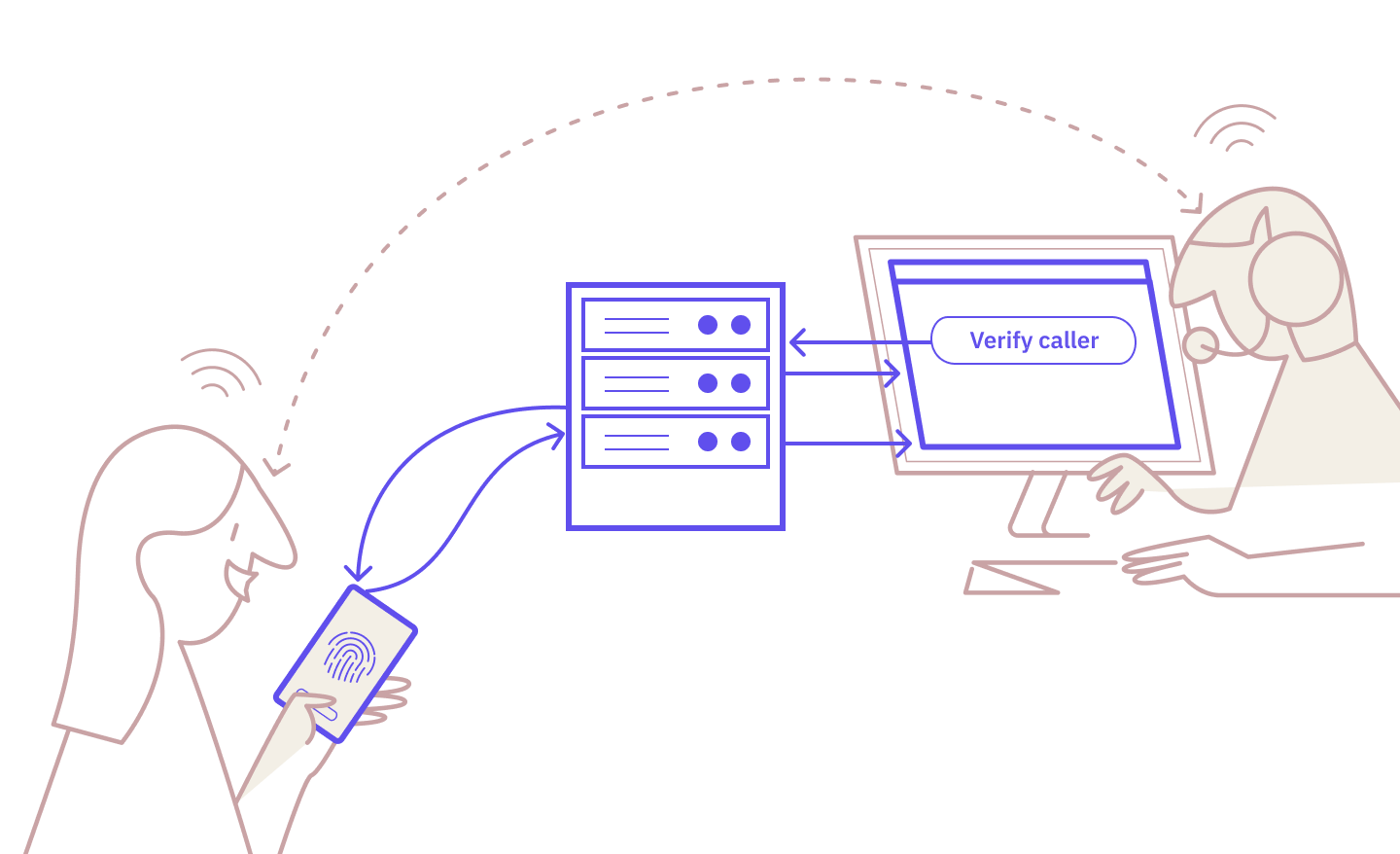
Here’s how the process looks:
- The agent triggers the authentication request.
- The caller receives the request in their eID app and verifies on their device.
- The agent sees the verified status, and the call continues.
It’s familiar, straightforward, and robust.
For a more comprehensive look, read: “How Exactly Does Caller Authentication Work?”
Caller authentication vs. security questions: side-by-side
The two methods are very different when it comes to the most critical considerations:

In short, eID caller authentication delivers better security and fraud resistance while also improving the customer experience.
When do security questions still make sense?
The truth is: They almost never do.
Knowledge-based authentication methods like security questions are rapidly becoming obsolete. They’re frustrating for callers and vulnerable to fraud. This makes them a poor way to verify people’s identity, regardless of which industry you operate in.
The only reason to still rely on security questions is if you haven’t yet managed to implement other verification methods and operate in a market where eIDs are not widely available.
If your callers already have access to eIDs, there’s no good reason to keep asking them about their first pet.
The next step
Security questions are a relic of the past.
Despite their name, they were never designed to be secure but to be easy to implement. For a while, that was the best that most companies could do.
But now that stronger caller authentication methods are available, your callers expect better.
eID-based caller authentication lets you verify someone’s identity in a highly secure, traceable way while building trust with customers and removing friction.
If you’re ready to move beyond security questions, we can help you get started.
Ready to make your service calls safer and simpler?
Caller authentication is already available with Norwegian and Swedish BankID, with the Danish MitID coming soon.
Start testing for free today or contact our sales team to learn more.
These Related articles

Zero Friction = Zero Assurance: The Case for eID Caller Authentication
Caller Authentication: Idura Launches New Identity Solution with MobilePay
