Caller Authentication vs. National ID Numbers
By Daniel Gniazdo on 19 March 2026
2 min read

Organizations often use a person’s national ID number to identify and verify a caller.
But knowing someone’s national ID doesn’t prove that you’re that person. Social security details can be seen or overheard in person or leaked in mass data breaches.
eID-based caller authentication is a more reliable way for a person to prove their identity.
Let’s look at how eID caller authentication works and compare it to national ID numbers.
How verification with national ID numbers works
In a typical scenario, the person will be asked to punch in their national ID number on the dialpad before being routed to an agent.
This is often the case in doctors’ offices, banks, and insurance companies.
The system then matches typed details to a customer record, so the agent can pull up relevant history and case files.
This approach is effective at helping to narrow down specific customers, but it does little to confirm whether the caller is actually that person. As a result, this method risks exposing sensitive information to any third party with access to a person’s national ID number.
How eID caller authentication works
eID-based caller authentication relies on national eID apps that most citizens already use.
Here’s how the process looks:
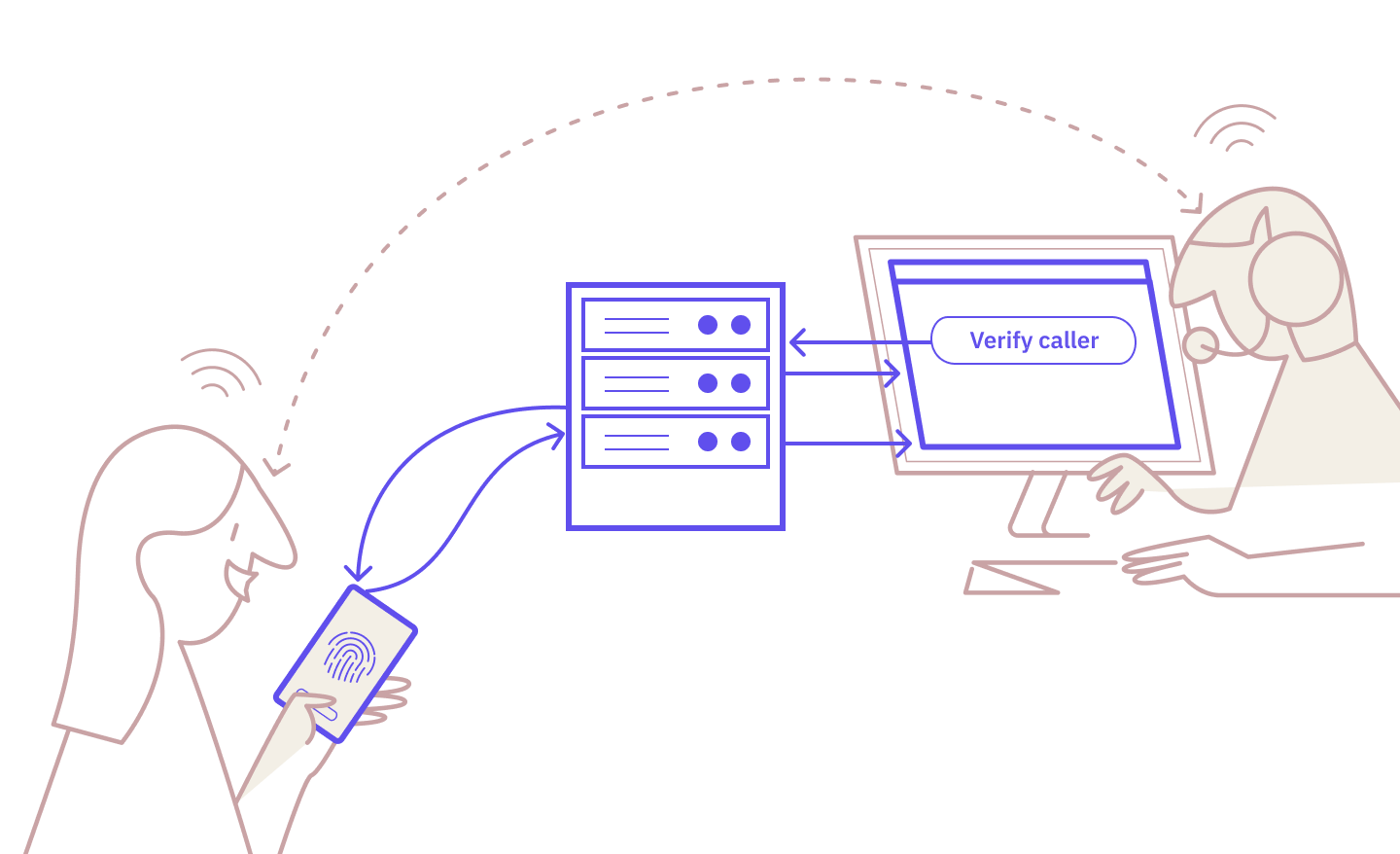
- The agent triggers the authentication request.
- The caller receives the request in their eID app and verifies on their device.
- The agent sees the verified status, and the call continues.
It’s familiar, straightforward, and robust.
For a more comprehensive look, read: “How Exactly Does Caller Authentication Work?”
Caller authentication vs. national ID numbers: side-by-side
Let’s look at how the two methods compare across different dimensions.
|
National ID Numbers |
eID Caller Authentication |
|
|
Security strength |
Low: Static number not directly bound to the person providing it |
High: eID-based cryptographic verification |
|
Fraud resistance |
Weak: Easy to overhear, see on a card, and expose in data breaches |
Strong: Requires the caller’s physical device and eID app |
|
Audit trail |
Weak: Logs the entered number but can’t trace who typed it |
Strong: Cryptographic proof of verification (who and when) |
|
Caller experience |
Positive: Quick to type on the dialpad while on hold for an agent |
Neutral: Familiar eID-based flow with a few extra steps |
|
Verification speed |
Fast: Seconds to enter on the dialpad |
Fast: Seconds from the agent triggering to the caller verifying |
|
Implementation effort |
Low: Record the IVR prompt and set up the database lookup |
Moderate: Integration with an eID provider via API or broker |
|
Customer type |
Existing only: Must match the number to a customer record |
Existing and new: Anyone with an eID can be verified |
When do national ID numbers make sense?
National ID numbers are useful for identification.
They help an agent quickly match a specific person to the relevant record, and typing them in doesn’t require much effort from the caller.
The problem is that identification and verification aren’t the same thing.
The national ID number tells the agent which account to look at, but it doesn’t conclusively prove the caller’s identity. Anyone with access to the number can easily provide it in place of the person it belongs to.
For an organization already using national ID numbers this way, the solution is to pair it with an additional verification layer.
The next step
By design, eID caller authentication provides that verification layer.
It supplements national ID-based record matching with secure, traceable verification that relies on the customers' existing eID apps.
This lets your organization get the best of both worlds: Accurate customer records linked to national ID numbers and fraud-resistant verification powered by eIDs.
If you’re thinking of adding verification to your call flow, we can help you get started.
Ready to make your service calls safer and simpler?
Caller authentication is already available with Norwegian and Swedish BankID, with the Danish MitID coming soon.
Start testing for free today or contact our sales team to learn more.
These Related articles

Zero Friction = Zero Assurance: The Case for eID Caller Authentication
Caller Authentication: Idura Launches New Identity Solution with MobilePay
