Caller Authentication vs. PINs
By Daniel Gniazdo on 26 March 2026
3 min read

Personal identification numbers (PINs) are a classic verification method.
Customers pick (or are assigned) a numeric code upon account creation, then type it in when calling the company.
PINs are familiar and convenient, but they come with tradeoffs.
Let’s see how PINs compare to eID-based caller authentication.
How PINs work
When a customer calls in, they’re prompted to enter a personal PIN to confirm their identity, most often through an IVR menu before reaching the agent.
The caller enters the PIN on the dialpad, and the system matches the digits against the stored code. If the numbers match, the customer gets through.
If there’s a mismatch because the caller forgot or mistyped the PIN, the call will get stuck.
This is a recurring frustration with PINs. It’s easy enough to remember a PIN for a credit card you use daily. But what if you have to recall a four-digit code you set up for an insurance company two years ago?
That’s why call centers run into customers struggling to remember their PINs.
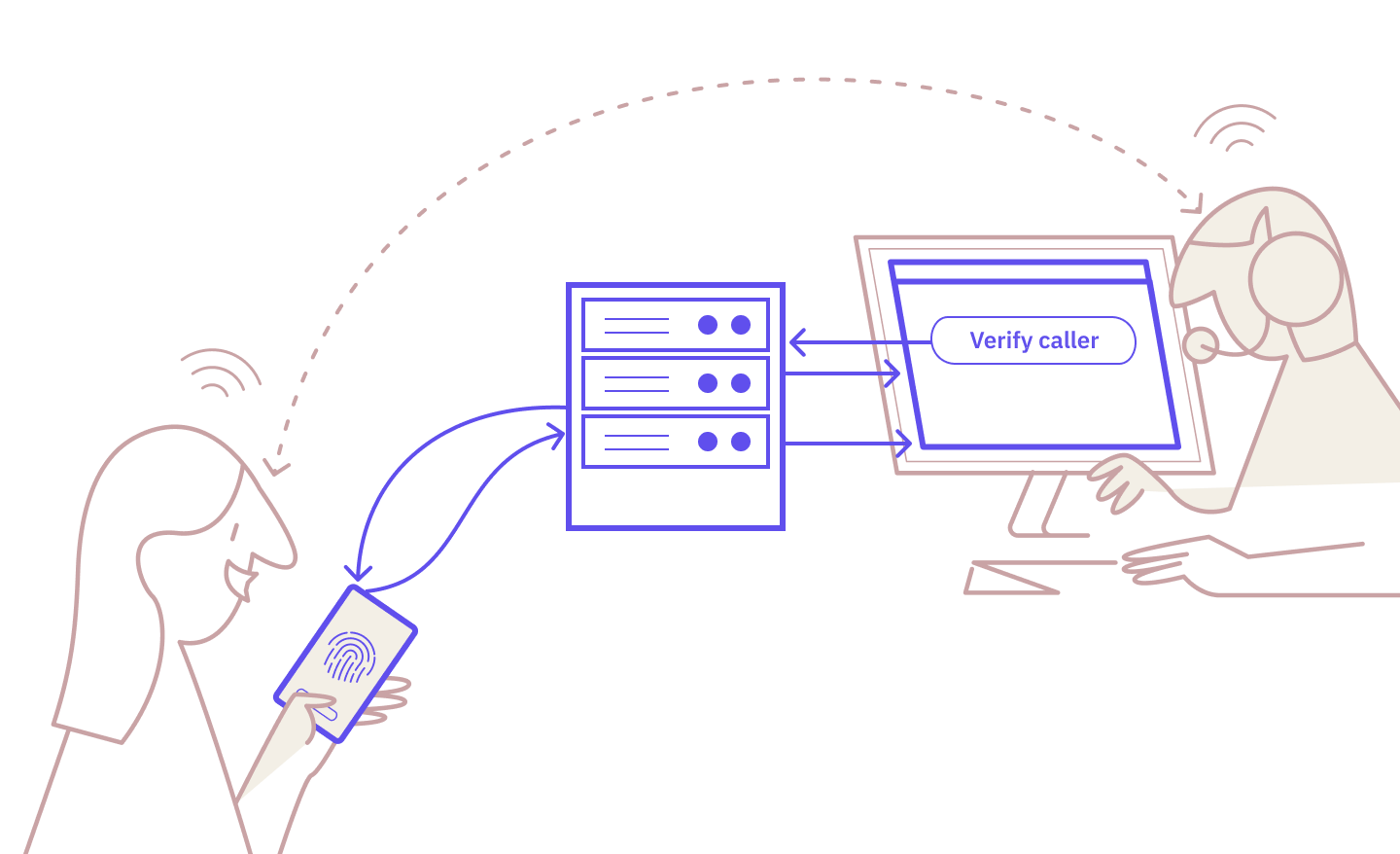
How eID caller authentication works
eID-based caller authentication relies on national eID apps that most citizens already use.
Here’s how the process looks:
- The agent triggers the authentication request.
- The caller receives the request in their eID app and verifies on their device.
- The agent sees the verified status, and the call continues.
It’s familiar, straightforward, and robust.
For a more comprehensive look, read: “How Exactly Does Caller Authentication Work?”
Caller authentication vs. PINs: side-by-side
How do the two verification methods compare?
|
PINs |
eID Caller Authentication |
|
|
Security strength |
Low: Static codes that are vulnerable to guessing and leaks |
High: eID-based cryptographic verification |
|
Fraud resistance |
Weak: Can be shared, seen, or guessed, and are often reused |
Strong: Requires the caller’s physical device and eID app |
|
Audit trail |
Weak: Logs that a PIN was entered, but not who typed it in |
Strong: Cryptographic proof of verification (who and when) |
|
Caller experience |
Neutral: Quick to type in, but can delay the call if forgotten |
Neutral: Familiar eID-based flow with a few extra steps |
|
Verification speed |
Fast: Seconds to enter on the dialpad |
Fast: Seconds from the agent triggering to the caller verifying |
|
Implementation effort |
Low: Just a way to store and match PINs per customer |
Moderate: Integration with an eID provider via API or broker |
|
Customer type |
Existing only: Need an account to match the pre-assigned PIN to |
Existing and new: Anyone with an eID can be verified |
When do PINs still make sense?
PINs are a minor step up from security questions.
They’re not as easy to link to a person’s background, and they’re quick to punch in without going through an awkward Q&A step with a call center agent.
But they suffer from the same issues as every other knowledge-based method.
First, knowing a secret code doesn’t prove identity. Any party with access to someone’s PIN can use it on a call.
Second, PINs are far from secure: Some people may use their birthday details, others may simply repeat the same digit four times. The five most common four-digit codes account for 20% of all PINs. It certainly doesn’t help that people tend to reuse the same PIN across multiple services.
Where PINs still hold up is as a secondary security layer in multifactor authentication. For instance, a caller may first have to provide their fixed PIN before receiving a one-time password.
PINs can also make sense for low-risk scenarios where a simple security check is sufficient and where the caller uses their PIN regularly enough to remember it.
But as a primary verification method, PINs are no longer enough in a climate of increasing fraud and falling customer trust.
The next step
PINs have served as a reliable default for a long time.
They’re simple, familiar to callers, and cheap to implement and maintain. But this convenience comes at a cost: Personal codes, no matter how strong, are susceptible to social engineering and data breaches.
eID-based caller authentication takes a different approach. Instead of asking callers to share a static secret, it lets them confirm their identity directly on their own device. This means your customers don’t have to remember any codes, and you also get a cryptographic record after someone’s verified.
If your organization still relies on PINs, eID caller authentication is an upgrade that provides stronger security without adding significant friction.
Ready to make your service calls safer and simpler?
Caller authentication is already available with Norwegian and Swedish BankID, with the Danish MitID coming soon.
Start testing for free today or contact our sales team to learn more.
These Related articles

Zero Friction = Zero Assurance: The Case for eID Caller Authentication
Caller Authentication: Idura Launches New Identity Solution with MobilePay
